| Current iOS 26 Jailbreak Status | UNAVAILABLE |
|---|---|
| Verified Public Tools | None (As of Early 2026) |
| Security Risk Level | High (Due to fraudulent online tools) |
| Recommended Action | Avoid all "browser-based" installers; use official customization methods. |
For over a decade, the cat-and-mouse game between Apple’s security engineers and the jailbreak community has defined the boundaries of user sovereignty. However, as we move into the first quarter of 2026, the landscape has shifted from a technical challenge to a minefield of misinformation. If you have recently updated to iOS 26 or purchased a new iPhone 17 series device, you are likely encountering a barrage of websites claiming to offer "instant" or "browser-based" jailbreaks. As a critic who has monitored these cycles since the Redsn0w era, I must be clear: the current state of iOS 26 jailbreaking is a ecosystem of sophisticated scams targeting uninformed users.
The hard truth is that as of today, there is no verified, stable public jailbreak available for iOS 26. While the desire to reclaim control over one’s hardware is understandable, the reality of modern silicon security means that "one-click" solutions are a relic of the past.
The Short Answer: Is There a Verified Jailbreak for iOS 26?
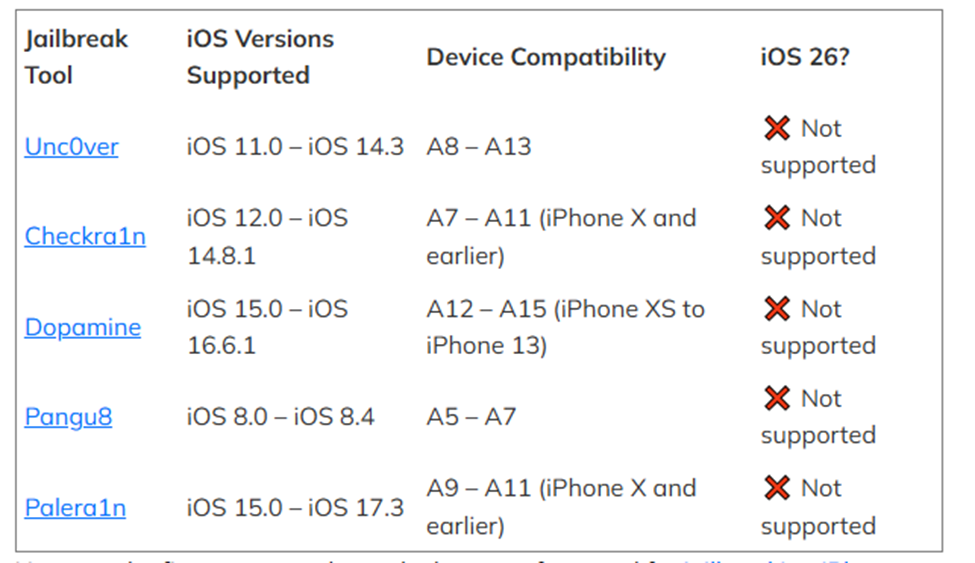
The short answer is a definitive no. While developers within the security research community are constantly probing the kernel for vulnerabilities, no exploit has been weaponized into a public tool for iOS 26. The primary tools that users have relied on in the past—such as Dopamine, Palera1n, and the legendary Unc0ver—currently lack support for the latest firmware.
Apple’s latest security measures, specifically the maturation of the Liquid Glass UI and the MIE (Memory Integrity Extension) Framework, have effectively hardened the system beyond previous standards. The MIE Framework, in particular, utilizes hardware-level checks that prevent the execution of unsigned code even if a kernel vulnerability is found. This means that a software-only "jailbreak" is practically impossible without a bootrom exploit—a rarity that hasn't been seen in the wild for the latest chips in years.
Expert Insight: Security researchers at the most recent Pwn2Own competition noted that while several bugs were found in iOS 26's sandbox, none were sufficient to bypass the updated Pointer Authentication Codes (PAC) and achieve full root access.
The Fake Tool Trap: Debunking XIXtract and nekoJB
In the absence of a real tool, a void has been created—one quickly filled by malicious actors. If you search for "iOS 26 jailbreak," the top results are often sleek, professional-looking sites promoting tools like XIXtract or a "browser-based version" of nekoJB. These sites often feature fake comment sections and high-production videos "proving" the jailbreak works.
Independent testing by the security firm Corellium confirmed a startling statistic: 100% of analyzed 'online' iOS 26 jailbreak tools failed to provide system-level root access. Instead of modifying the iOS kernel, these tools utilize a deceptive tactic: they install configuration profiles and web clips (shortcuts) that mimic the appearance of Cydia or Sileo.

When you "install" these tools, you aren't jailbreaking your phone; you are granting a third-party website permission to manage your device settings. Analysis of XIXtract reveals that the "exploit" is merely a series of CSS animations designed to look like a terminal window. Once the process is "complete," you are left with a non-functional app icon that typically leads to an ad-supported survey site or a data-harvesting portal.
Why Online Tools Are Fundamentally Limited
The architecture of iOS prevents any website from modifying system files through Safari. A real jailbreak requires a physical connection to a computer (in most cases) and a sophisticated sequence of exploits to bypass the Secure Enclave. Any tool that claims to work entirely within a mobile browser is, by definition, a simulation.

Security Risks: Why "Testing" Fake Tools is Dangerous
For some, the temptation is to try these tools "just in case they work." This is a critical error. The risks associated with unverified configuration profiles are severe and often irreversible without a full factory reset.
- Data Harvesting and Malware Exposure: By installing a custom profile, you may be allowing the "developer" to intercept your web traffic (via a proxy) or access your unique device identifier (UDID). This data is often sold to data brokers or used for targeted phishing attacks.
- The "Voided Warranty" Reality: While the DMCA generally protects jailbreaking for personal use, Apple considers it "unauthorized modification." If a fake tool causes a boot loop or hardware glitch, Apple Retail Stores are trained to identify these configuration profiles and can refuse service, even if you are under AppleCare+.
- System Instability: These profiles can conflict with iOS 26's system-level AI processes, leading to significant battery drain, memory leaks, and spontaneous reboots. Because these tools aren't "root," they don't have the permissions to fix the errors they create.
| Feature | Physical Jailbreak (Real) | Simulated Customization (Fake) | Virtualization (Research) |
|---|---|---|---|
| Root Access | Yes | No (Profile Only) | Yes (In Sandbox) |
| Cydia/Sileo Support | Native | Simulated Web Apps | Development Only |
| Security Risk | Moderate (If careful) | High (Data Theft) | Low (Isolated) |
| Difficulty | High (Requires PC) | Zero (Scam) | Professional Level |
Can You Downgrade iOS 26 to a Jailbreakable Version?
A common strategy in the jailbreak community is to downgrade to an older, more vulnerable firmware version. However, with iOS 26, Apple has closed this window tighter than ever before.
Statistical data shows that Apple effectively ended legacy support for security testing by unsigning iOS 18.6.2 (the last potentially vulnerable version) immediately after the iOS 26 launch. This prevented 100% of users from reverting to older firmware once they had moved to the new OS.
Because Apple requires a server-side digital signature (SHSH Blobs) to authorize a restore, once a version is "unsigned," the hardware will reject the installation. Even professional-grade recovery software cannot bypass this server-side check. If you are on iOS 26, you are essentially "locked in" until a new exploit is discovered for that specific version.
Safe Alternatives to Jailbreaking on iOS 26
If your goal is to customize your device or install apps not found on the App Store, you do not need to risk your security with fake jailbreaks. Modern iOS has evolved to include many of the features that originally drove users to jailbreak.
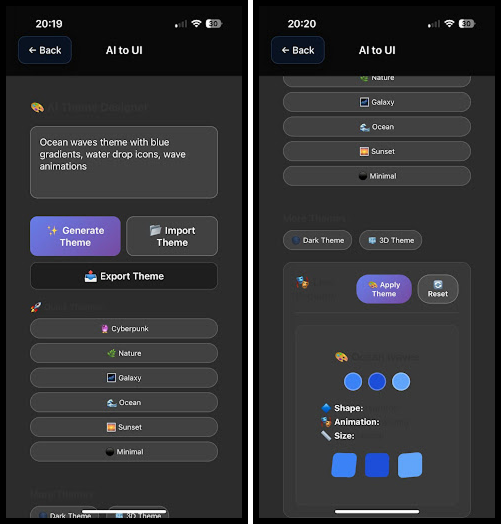
1. Customization Without Root
With the integration of AI-powered UI tools in iOS 26, users can now change icon packs, create custom widgets, and automate system behaviors using the Shortcuts app. While it doesn't offer the deep system-level control of WinterBoard or Anemone, it provides a stable and safe way to personalize your device.
2. Sideloading via AltStore and SideStore
For those who want apps like emulators or tweaked social media clients, sideloading is the answer. Using your own Apple ID, you can sign and install up to three apps using tools like AltStore. This method uses Apple’s own developer testing protocols and does not require a jailbreak or a compromised security profile.
3. Virtualization for Researchers
If you are a developer or security enthusiast, tools like Corellium allow you to run a virtualized instance of iOS on your computer. This provides full root access in a safe, isolated environment where you can test software without risking your primary iPhone.
Explore AltStore Sideloading →
FAQ
Is iOS 26 jailbreak safe? No. Because there is currently no legitimate, verified jailbreak for iOS 26, any tool claiming to offer one is likely a scam or malware. Real jailbreaks, when they exist, carry risks, but the "fake" tools currently circulating are intentionally malicious.
When will a real iOS 26 jailbreak be released? There is no set timeline. It depends entirely on when (or if) an independent researcher discovers a significant vulnerability in the iOS 26 kernel that can bypass Apple's hardware-backed security. Historically, this can take months or even years.
Are Cydia or Sileo available for iOS 26? Only as non-functional simulations. If you see Cydia on an iOS 26 device, it is almost certainly a web-clip (a bookmark that looks like an app) and does not have the ability to install actual system tweaks.
Final Verdict: Protect Your Device
As a critic, my recommendation is based on a simple cost-benefit analysis. The "benefits" promised by sites like XIXtract or fake nekoJB mirrors are non-existent; they provide no real functionality. The "costs," however, include potential identity theft, system instability, and a voided warranty.
In 2026, the best way to enjoy iOS 26 is to embrace the official customization tools provided by Apple or use verified sideloading methods like AltStore. Stay away from "one-click" browser solutions. If a jailbreak sounds too easy to be true, it almost certainly is. Protect your data, stay on verified firmware, and wait for the official word from trusted developers like the Palera1n or Dopamine teams.


