Quick Facts
- Breach Date: April 13, 2026.
- Data Exposed: Names, email addresses, phone numbers, and reservation IDs.
- Platform Impact: Over 100 million active users at risk.
- Primary Threat: High-value phishing and Account Takeover (ATO).
- Reset Requirement: Booking.com has reset reservation PIN numbers for all affected customers.
- Economic Risk: Stolen hotel accounts are trading for up to $5,000 on criminal forums.
- Recommended Action: Implement 15+ character passphrases and multi-factor authentication immediately.
Booking.com confirmed a major data breach on April 13, 2026, exposing guest PII and reservation details. Protecting your account requires immediate data breach protection measures. Follow these 5 steps to recover your account security and prevent identity theft.
The 2026 Booking.com Incident: What Went Wrong
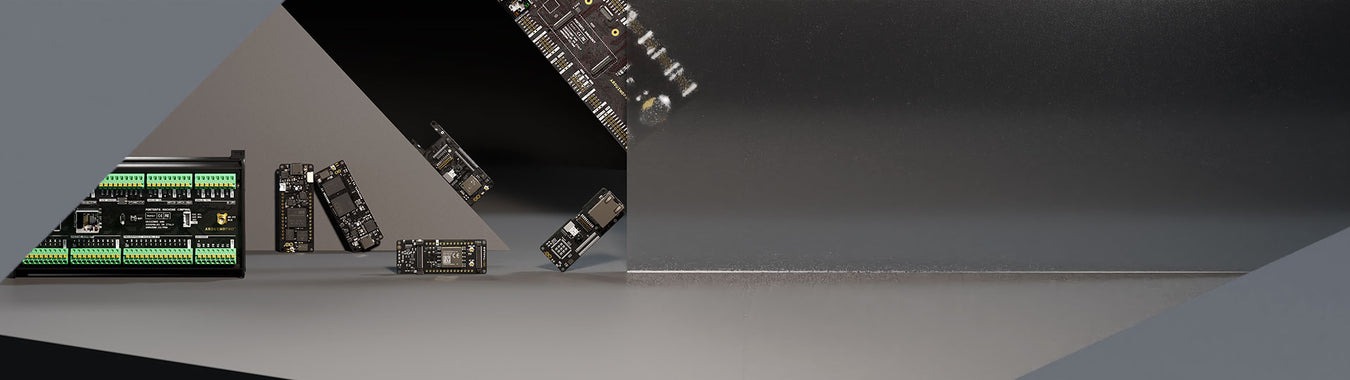
The digital travel landscape was shaken on April 13, 2026, when Booking.com confirmed a security breach involving unauthorized access to guest booking information. This was not a direct hack of the central Booking.com database, but rather a sophisticated exploitation of hotel portals through targeted malware. By infiltrating the property management systems of individual hotels, cybercriminals gained a direct window into guest reservation data, including names, contact details, and specific travel dates.
The impact of data breach on individuals goes far beyond a simple leaked password. In this instance, the stolen accounts have been observed selling for as much as $5,000 on criminal forums like LolzTeam. This high valuation stems from the richness of the data; knowing exactly when and where a high-net-worth individual is traveling provides the perfect foundation for social engineering. This event marks a significant point in the history of data breach examples within the travel industry, highlighting how online travel agencies (OTA) are increasingly viewed as gold mines for identity thieves.
Criminals use this information to launch credential stuffing attacks or to facilitate fraudulent transactions. When your reservation ID and hotel communication history are in the hands of a third party, they can craft messages that are indistinguishable from official hotel outreach. This level of access allows for highly effective account takeover (ATO) maneuvers where the attacker can change booking details or redirect payments to their own accounts.
| Incident Year | Breach Type | Primary Impact | Mitigation Measure |
|---|---|---|---|
| 2023 | Phishing Surge | 900% increase in attacks | User education |
| 2024 | Credential Stuffing | Unauthorized login attempts | Forced password resets |
| 2026 | Hotel Portal Malware | Exposure of PII and reservation IDs | Resetting all reservation PINs |
Following the discovery of the 2026 breach, Booking.com reset the reservation PIN numbers for all affected customers as a precautionary security measure. However, a PIN reset is only the beginning of a comprehensive recovery strategy. If you are wondering how to check if booking.com account is compromised, look for unauthorized changes in your upcoming trips or unexpected emails confirming "successful" login attempts from unknown devices.
5 Critical Steps for Data Breach Protection
After an incident of this scale, the burden of security often shifts to the user. To maintain high cybersecurity hygiene, you must move quickly to close the windows of opportunity for hackers.
1. Upgrade to 15+ Character Passphrases
The foundation of data breach protection is a strong, unique password. Traditional passwords like "Summer2026!" are easily cracked by modern generative AI tools used by cybercriminals. Instead, switch to a passphrase that is 15+ characters long. Use a string of random words that are easy for you to remember but impossible for a machine to guess. Ensure this passphrase is used only for Booking.com and nowhere else to prevent the risks associated with credential stuffing.
2. Enable Multi-Factor Authentication (MFA)
Securing hotel booking accounts with two-factor authentication is the single most effective way to block unauthorized access. Even if a hacker has your email and passphrase, they cannot enter your account without the secondary code sent to your physical device. Always opt for an authenticator app rather than SMS-based codes if possible, as SIM-swapping is a common tactic in travel-related identity theft.
3. Review Active Sessions and Reset Internal PINs
Go to your account settings and review the list of "Active Sessions" or "Logged-in Devices." If you see a login from a city you haven’t visited or a device you don’t own, terminate that session immediately. Additionally, ensure you have acknowledged the reservation PIN reset. These PINs are often used when communicating with the hotel directly or making changes at the front desk; having a fresh, uncompromised PIN is vital.
4. Monitor for 'Vacant Home' Signals
One of the most dangerous aspects of the impact of data breach on individuals is the physical risk. If a criminal knows you are traveling from June 10th to June 20th, they know your primary residence is likely empty. This is why securing your travel itineraries is a matter of home security. Ensure your home security systems are active and avoid sharing your specific travel dates on social media, especially after your data has been leaked.
5. Scrutinize WhatsApp and SMS for Spear Phishing
One of the most effective 8 ways to prevent data breaches from escalating is to verify all incoming communications. We have seen a 900 percent surge in travel-related phishing attacks between 2023 and 2024, and the 2026 breach has only accelerated this trend. Scammers will use the stolen reservation data to send you urgent messages via WhatsApp or SMS, claiming there is a problem with your payment and providing a link to "fix" it. Never click these links. Always go directly to the official Booking.com website or app to handle payment issues.
Beyond the App: Protecting Your Identity and Home
Securing your account is a critical first step, but protection from data breach requires a longer-term view of your digital footprint. When personally identifiable information (PII) like your phone number and email are leaked, you become a permanent target for social engineering. Criminals may use this data months later, hoping you have lowered your guard.
Consider utilizing dark web monitoring services. These tools scan criminal marketplaces to see if your specific credentials are being traded. If you receive an alert, it is a sign that you need to change passwords for all linked accounts immediately. Furthermore, since your name and contact details were part of the 2026 leak, you should be on high alert for identity restoration needs.
Fraudulent transactions often follow these breaches. You should utilize card controls through your banking app. Most modern banks allow you to "freeze" your card or set strict spending limits for international transactions. By setting these parameters before you travel, you create a safety net that prevents a stolen booking account from draining your bank balance.
For European travelers, the GDPR provides specific rights regarding your data. You have the right to ask Booking.com exactly what data was exposed and how they are remediating the situation. Understanding these legal frameworks is an essential part of data breach protection measures in the modern era.
Official Recovery Resources and Expert Tools
If you believe your identity has been stolen as a result of the Booking.com breach, you should immediately turn to official government resources. IdentityTheft.gov is the gold standard for creating a recovery plan. They provide step-by-step guidance on how to report the theft and clear your credit record.
For technical guidance on securing your broader digital life, the Cybersecurity & Infrastructure Security Agency (CISA) offers comprehensive manuals on cybersecurity hygiene. They emphasize that data breach protection is not a one-time event but a continuous process of monitoring and updating.
- IdentityTheft.gov: Use this for reporting and creating a recovery path.
- CISA.gov: Reference their "StopRansomware" and "Phishing Awareness" guides.
- Banking Apps: Use the "Transaction Alerts" and "Geographic Blocking" features.
By combining these expert tools with the specific 2026 recovery steps, you can significantly reduce the impact of the breach and travel with greater peace of mind.
FAQ
How can you protect yourself from data breaches?
Effective data breach protection requires a multi-layered defense. Start by using a dedicated password manager to ensure every online account has a unique, complex passphrase. Enable multi-factor authentication on all sensitive accounts, especially those related to finances and travel. Finally, stay informed by checking services that track leaked data and be skeptical of any unsolicited communication that asks for personal information or immediate payment.
Can I check to see if my SSN has been compromised?
While the 2026 Booking.com breach focused on reservation data, your Social Security Number (SSN) can be exposed in other large-scale leaks. You can check your credit reports for free at AnnualCreditReport.com to look for any accounts you didn't open. Additionally, many identity theft protection services offer specific monitoring for your SSN across the dark web and public records.
What if my SSN was part of a data breach?
If your SSN is compromised, you should immediately place a credit freeze on your accounts at the three major credit bureaus: Equifax, Experian, and TransUnion. This prevents anyone from opening new lines of credit in your name. You should also file a report with the FTC at IdentityTheft.gov and monitor your existing financial accounts closely for any suspicious activity.
Is idx a reputable company?
Yes, IDX is a well-established player in the identity protection and data breach response industry. They are frequently contracted by large organizations and government agencies to provide identity monitoring and restoration services to individuals affected by data breaches. They offer tools for credit monitoring, dark web scanning, and access to identity restoration experts.